
|
Date: July 15.13:47:11 2022 Source : doksi.net/en |
This article is about the reasons companies are always forced to extinguish the flames in Shadow IT, how they can study the root cause while struggling with their internal IT and why they still believe in the suppliers’ mirage.
Background
If you are familiar with the expression of “extinguishing the fire” and “shadow IT”, please move on to “The New IT Management Triangle” section of this article. If you are not, let’s cover these terms first.
Extinguish the flames expresses a kind of situation where there is a frightening event or action in that you are forced to act immediately against the extension of the issue. You are bound to minimize your loss and save the status quo. This term is usually bound up with the expression of crisis management, Incident Management or sometimes disaster mostly in Critical IT Infrastructures. One of the most commonly-used terms that come up in working with developers or a DevOps engineers in Business Owned IT.
Shadow IT refers to software, services or IT devices outside the control and ownership of formal IT within the organization. If you see the description at Cisco, you will find this definition: “the use of IT-related software or hardware by an individual or a department even though IT or IT security group is not cognizant of these services, software, and hardware operating beyond the IT standards within the organization”.
To become familiar with Shadow IT you have to learn the main drivers, aspiration of players and main concerns in the context of IT department, business departments and contractors.
The New IT Management Triangle
The main intention of modern IT departments is usually to operate in a future-proof way, where business players can work together with agility in a cost-effective way. Being future-proof, cost-effective and agile might be the new management triangle in IT management.
To get a deeper understanding let’s analyze these three phrases below:
- Future-proof IT or software means having the ability to follow the rapid change in user- and business demands regarding life-cycle costs, wholesome mix of contractors, transparent technical solutions and deliberate strategy of IT governance.
- Being cost-effective means not spending more than what is actually needed in a certain period of time. This way not only the implementation cost of a project should be a factor to consider but the IT solution as a whole: from the cost of maintenance, environment management, through licensing policy to the cost of replacement. The cost of changing vendors could also be a risk we want to express in money.
- Agility in IT refers to adaptability and the ability to act and fulfill business demands quickly. It’s worth mentioning that there is no reason to confuse the term “agility” with agile project management. The latter is more like a fancy and popular buzzword to describe a way of thinking which goes with predefined measures like sprints, product backlog, story-points, release planning and so on. In IT infrastructure agility means to ease the process of introducing a new IT solution, and fulfill business demands quickly in a flexible way by reducing bureaucratic measures.
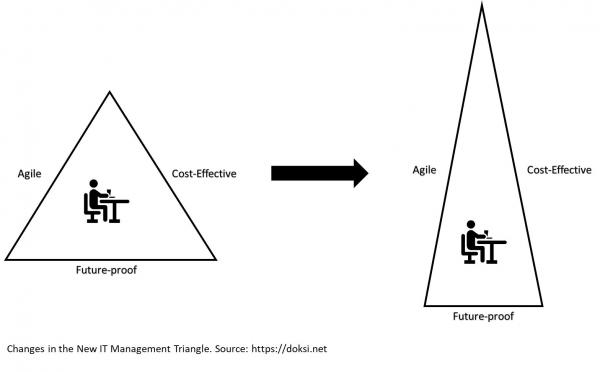
Changes in the New IT Management Triangle
Hidden Risk in Business Owned IT
Sometimes business departments - with a little insight into the IT management triangle – are not really satisfied with the cost and time requirements of IT solutions provided by the IT department within the organization. If the total cost of an IT solution is separated and charged other business departments, clients (who use that solution) might think that it does not worth the money compared to other IT solutions seen on fancy PPTs presented by an IT sales representative. Sometimes it’s true but usually it doesn’t.
Business departments having their own IT budget at their disposal are tempted somedays to implement or introduce a new a software solution with some time- and financial limitations. And that’s the crux of IT Governance that IT consultants are crazy about! No consideration of the total cost of ownership (TCO) and sometimes lack of IT security gives you the greatest opportunity to save the client a few pennies in a short run and charge inner IT thousands of dollars eventually.
Why? In business owned IT, emphasis easily shifts from being future proof to business agility and flexibility, which puts internal IT under strain to meet business demands within a rigid IT architecture. When it fails, business leaders start to keep slack rein on IT and contractors (making shadow IT as an alternative), and focus on short time gains.
Sometimes systems or services within shadow IT grow too big, which goes with too much the company does not intend to take anymore. When this happens, owners of shadow systems often forced to involve IT in and find a new owner. This can arise complicated political aspects, strategical deliberations all acting in the backstage.
In modern organizations, preferably in the telco and banking sector, state of the art technologies can only succeed within the IT departments controlled by rigorous IT standards. Consultants can help, but never let your business out of your hand! The biggest challenge is vendor lock-in, while managing “strategical partnerships”, meaning big exposure to contractors and hard ways to step back.
All in all, it’s recommended to create a corporate setting where some parts of the IT budget is owned by business departments that could be spent via internal IT. That is the greatest quality assurance to have the IT involved in the first step.
To dig deep for a little bit of insight about risk of shadow it, check out this short video:
Let’s have an example
A reporting leader within AA Bank aims to introduce a fancy MS BI tool, because the leader’s aspiration is to scale down operation within the department via reducing the lead time of creating reports. Sales representatives, supported by an MS specialist sells the vision of scaling down the department’s work via using the new solution. It’s truly recommended to draw the internal IT into conversation to see through the deception and understand the risk of inner adaptability and TCO in the long run. If internal IT owns the budget or business department owns it, but payment- and contracting processes take place through internal IT (or a centralized procurement), it’s much more likely that IT governance aspect wil be taken into consideration and there will be a well-founded SLA.
The Good Old IT Adage
There is an old adage among management consultants which tells you “There was nobody fired because of introducing IBM”. Technology behemoths give you the sentiment of safety and sail before the wind as a leader. Whoever would think that an Oracle / SAP / MS consultant is not whizz on introducing their product? The Truth is that we are all human and while organizational complexity has no limit, human comprehension has. Charging you thousands of dollars as a daily fee per a subcontractor does not mean your project is going to fly.
When Force of Habits is Stronger than Your Drive to Change
There is an old Hungarian adage that goes like this: if you snivel but do not change it doesn’t fluster you enough.
Companies with little insight into their own IT governance can easily deplete their future reserves. But acting against technical debts is a long-time investment which goes with short-term risks. That’s the main reason why leaders – staying only few years in a job – do not have the gut to struggle against these threats, until there is no way to get around.
Everybody knows that introducing a new technology needs new skills, sometimes new mindset that internal IT may lack at first. Here comes the term of “learning corporation” where technology savvy peers are honored in a proper way and counter actions and organizational change is well managed by top level leaders. If you want to get familiar with how corporate leaders in a politically affected environment can bring changes in IT organizations or want to learn the basic principles of counter moves and counter implementations then “Peter. G. W. Keen – Information Systems and Organizational Change“ is for you. It’s written at Massachusetts Institute of Technology (MIT) in 1981, but it’s still current and accurate! That’s why it became a fundamental reading of IT team leaders and college students learning Business Informatics or IT governance.
Only one thing is missing from the study that worth considering during hard times: “change the way you look at things and the things you look at change”. It can also create a more comfortable working environment.
Do you have a good idea? Write a guest post for us!
Recommended articles
Russian Perspective about the War in Ukraine
Nowadays there is no really impartial opinion neither in the Western media nor in the Russian news. While reading articles from both sides you may find information that can be quite contradictory.
Political Awareness in IT ManagementAs a first-time manager one of your responsibilities is to find ways to improve daily teamwork. People may cut you slack in the beginning, but remember: time won’t stop until you are ready. Teams rarely work alone, so your squad works in a project setting, with daily connection to several groups from various departments with different interests.
Recommended documents- Creating a StorageCraft ShadowProtect IT Edition 3Day ISO, How to Guide / 2021, 6 page(s)
- Shadowtraderpro FX Trader Users Guide / 2010, 7 page(s)
- In The Shadow of Russia, Romanias Relations with Moldova and Ukraine / 2000, 31 page(s)
- Communism Shadow, Post Communist Legacies, Values and Behavior / 2010, 44 page(s)
- Claessens-Pozsar-Ratnovski - Shadow Banking, Economics and Policy / 2012, 37 page(s)
Comments
| Anonymus | October 15, 2024 | |
|---|---|---|
| Neat! | ||
 Just like you draw up a plan when you’re going to war, building a house, or even going on vacation, you need to draw up a plan for your business. This tutorial will help you to clearly see where you are and make it possible to understand where you’re going.
Just like you draw up a plan when you’re going to war, building a house, or even going on vacation, you need to draw up a plan for your business. This tutorial will help you to clearly see where you are and make it possible to understand where you’re going.